Advanced Techniques - Mixed authentication
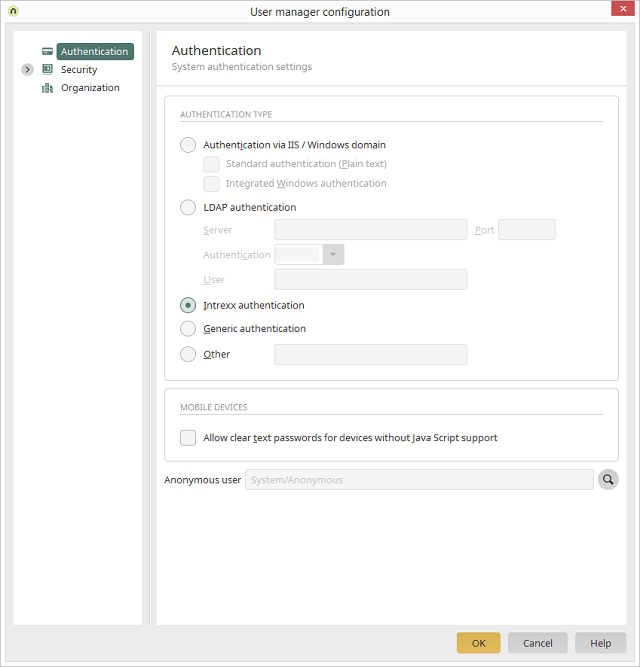
In the Users module, you can define different authentication methods for your portal via the Main menu: User/Configuration/Authentication:
- Intrexx authentication
- Single-Sign-On (Windows / ADS)
- LDAP authentication
-
Several users share a workstation in an intranet.
Solution: SSO + LDAP authentication, or SSO + Intrexx authentication -
Internal users access the portal by various methods from both internal and external locations.
Solution: SSO + LDAP or Intrexx authentication. -
An extranet where internal users access the portal using their Active Directory credentials.
Solution: LDAP + Intrexx authentication.
Customizations
Settings will need to be adjusted in the webserver configuration – Internet Information Services (IIS) or Tomcat. Our first example covers the amendments for IIS. It may also be necessary to setup or revise the configuration of a reverse proxy. Also, these two files in the Portal directory \internal\cfg directory will need to be customized:- LucyAuth.cfg
- om.cfg
Sample om.cfg file
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<authentication anonymous="05CE8CE3035924F7D3088895F1D87DADD65CFAE4">
<binding scope="odataservice" auth-type="IntegratedAuthClient"/>
<binding scope="web" auth-type="MyDemoAuth"/>
<binding scope="documentintegration" auth-type="IntegratedAuth"/>
<binding scope="client" auth-type="IntegratedAuthClient"/>
<binding scope="webservice" auth-type="IntegratedAuthClient"/>
<webserver-configuration plain-text-auth="false" integrated-auth="true" insecure-basic="false"/>
<mobile-devices plain-text-auth="never"/>
</authentication>
<security pwd-dictionary="....."/>
<organization default-container-guid="...."/>
</configuration>
Sample additional section for LucyAuth.cfg file
MyDemoAuth
{
de.uplanet.lucy.server.auth.module.integrated.IntegratedLoginModule sufficient
debug=false;
de.uplanet.lucy.server.auth.module.ldap.LdapBindLoginModule sufficient
java.naming.provider.url="ldap://directoryserver.example.org:389"
java.naming.security.Authentifizierung="simple"
java.naming.security.principal="$[DN]"
debug=false;
de.uplanet.lucy.server.auth.module.intrexx.IntrexxLoginModule sufficient
debug=false;
de.uplanet.lucy.server.auth.module.anonymous.AnonymousLoginModule sufficient
debug=false;
};
IIS Configuration changes
The solution demonstrated here uses an alternative URL for the second authentication method (in this case, Intrexx authentication). In the example shown, the portal URL is demo8, and the alternative URL is demo8_2. A configuration with just one URL would require an additional network card in the Intrexx portal server.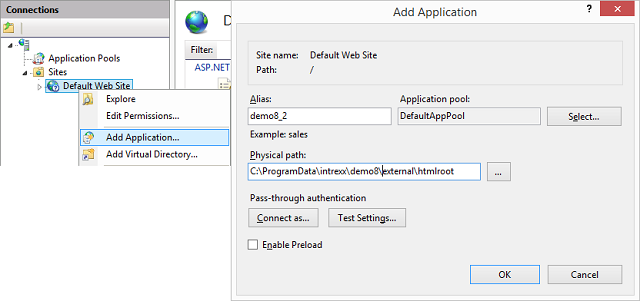
To setup the alternative URL, in the IIS Manager, under Connections, open the context menu of the Default Web Site and select Add Application.
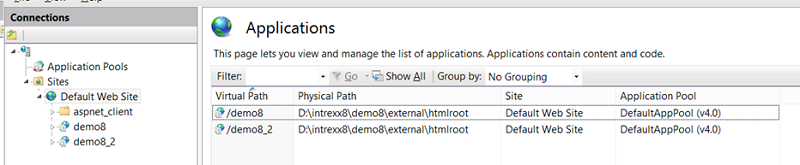
The two example applications have the same physical path. This will be the Portal directory \external\htmlroot.
ASP Configuration (for each website URL)
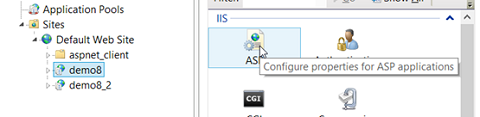
Open the ASP properties of demo8 by double-clicking on the ASP option in the middle area (Configure properties for ASP applications).
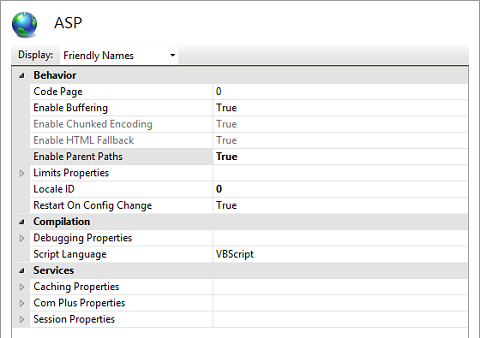
Define th property Enable Parent Paths = True. Repeat the change for demo8_2.
Authentication configuration for the portal URL demo8: SSO
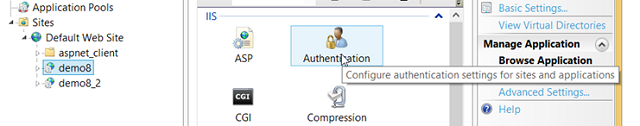
Open the authentication settings of demo8 by double-clicking on the Authentication option in the middle area (Configure authentication settings for sites and applications).
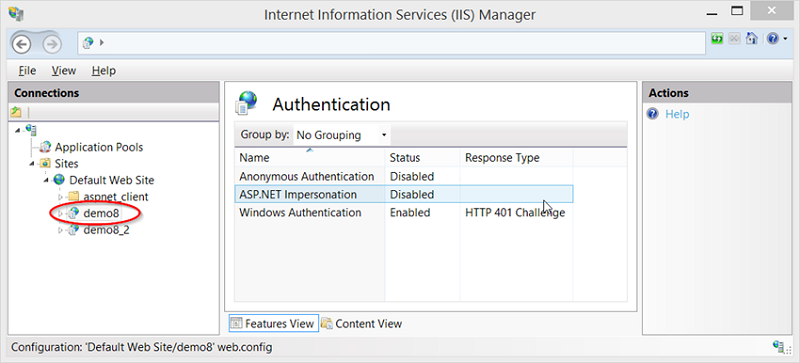
Apply the following settings:
- Anonymous Authentication = Disabled
- ASP.NET Impersonation = Disabled
- Windows Authentication = Enabled - HTTP 401 Challenge
Authentication configuration for the alternative URL demo8_2: Intrexx login
Open the authentication settings of demo8_2 by double-clicking on the Authentication option in the middle area (Configure authentication settings for sites and applications).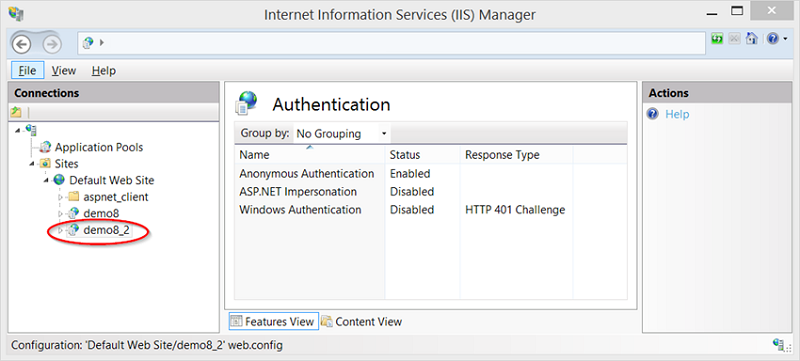
Apply the following settings:
- Anonymous Authentication = Enabled
- ASP.NET Impersonation = Disabled
- Windows Authentication = Disabled
Configuration with LDAP and Intrexx authentication
If the authentication methods LDAP and Intrexx are provided, both of the files LucyAuth.cfg and om.cfg need to be modified. The file LucyAuth.cfg should be adjusted as follows:MyDemoAuth2
{
de.uplanet.lucy.server.auth.module.ldap.LdapBindLoginModule sufficient
java.naming.provider.url="ldap://directoryserver.example.org:389"
java.naming.security.authentication="simple"
java.naming.security.principal="$[DN]"
debug=false;
de.uplanet.lucy.server.auth.module.intrexx.IntrexxLoginModule sufficient
debug=false;
de.uplanet.lucy.server.auth.module.anonymous.AnonymousLoginModule sufficient
debug=false;
};
java.naming.provider.url="ldap://directoryserver.example.org:389"java.naming.provider.url="ldaps://directoryserver.example.org:636"<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<authentication anonymous="05CE8CE3035924F7D3088895F1D87DADD65CFAE4">
<binding scope="web" auth-type="MyDemoAuth2"/>
<binding scope="client" auth-type="IntrexxAuth"/>
<binding scope="webservice" auth-type="IntrexxAuth"/>
<binding scope="odataservice" auth-type="ODataAuth"/>
<binding scope="documentintegration" auth-type="IntrexxAuth"/>
<webserver-configuration plain-text-auth="false" integrated-auth="false"/>
<mobile-devices plain-text-auth="never"/>
</authentication>
<security/>
<organization default-container-guid="..." default-distlist-guid="..."/>
</configuration>